vSphere 5 - What's New (and relevant for the VCP 5) (Part 1)
13 Nov 2011 by Simon Greaves
 vSphere 5 has been available for a couple of months now so now is an ideal time to look at upgrading your infrastructure and also to start the upgrade path for the VCP 4s out there to the VCP5. This is by no means a complete study guide, rather an introduction into the various new features and components of vSphere 5 over and above what was already available in vSphere 4. To really understand all the new features of vSphere 5 you need to work with it, so if you don’t have one already, go build a home lab. Any PC will do with VMware workstation as you can run virtual machine versions of ESXi, it is supported by VMware, you may need a RAM upgrade though. An alternative is to build a whitebox server. Ray Heffer has written a good whitebox home lab guide, I suggest checking it out if you are not sure where to start. Also check out the whitebox HCL at vm-help.com for ideas. The site only lists support for vSphere 4 and earlier but most components should work with ESXi 5.
vSphere 5 has been available for a couple of months now so now is an ideal time to look at upgrading your infrastructure and also to start the upgrade path for the VCP 4s out there to the VCP5. This is by no means a complete study guide, rather an introduction into the various new features and components of vSphere 5 over and above what was already available in vSphere 4. To really understand all the new features of vSphere 5 you need to work with it, so if you don’t have one already, go build a home lab. Any PC will do with VMware workstation as you can run virtual machine versions of ESXi, it is supported by VMware, you may need a RAM upgrade though. An alternative is to build a whitebox server. Ray Heffer has written a good whitebox home lab guide, I suggest checking it out if you are not sure where to start. Also check out the whitebox HCL at vm-help.com for ideas. The site only lists support for vSphere 4 and earlier but most components should work with ESXi 5.
vSphere 5 Enhancements
System Requirements
There have been a few changes in the requirements for installing and upgrading to vSphere 5. I am working on an upgrade guide which will contain further information on the steps required to perform an upgrade, but for now I will just go over the requirements. If you are eager to get installing then you can check out the vSphere Upgrade Guide.
Update Manager
Update Manager has been optimised for cluster remediation, rather than per host. It includes the ability to schedule a reboot after VMware tools have been installed or after a VM hardware upgrade. Support is also included for Update Manager download service 5.0 (UMDS 5.0) the command line driven update utility.
It also adds a nifty migrate ESX to ESXi function, allowing existing ESX servers to be migrated to ESXi without loosing all existing datastores and virtual machines. IVOBEERENS.NL has a guide explaining the steps involved.
It’s not all good news though as VMware have now removed VM patching functionality. Update manager needs to be installed on a 64-bit OS, like vCenter Server.
ESXi
vSphere 4.1 represented the last ESX version available. Now it is purely ESXi. ESXi is now a stateless OS, capable of running only in memory, removing the requirements for an existing local storage device. This is only possible when PXE booting using Auto Deploy. (Auto Deploy will be explained in part 3)
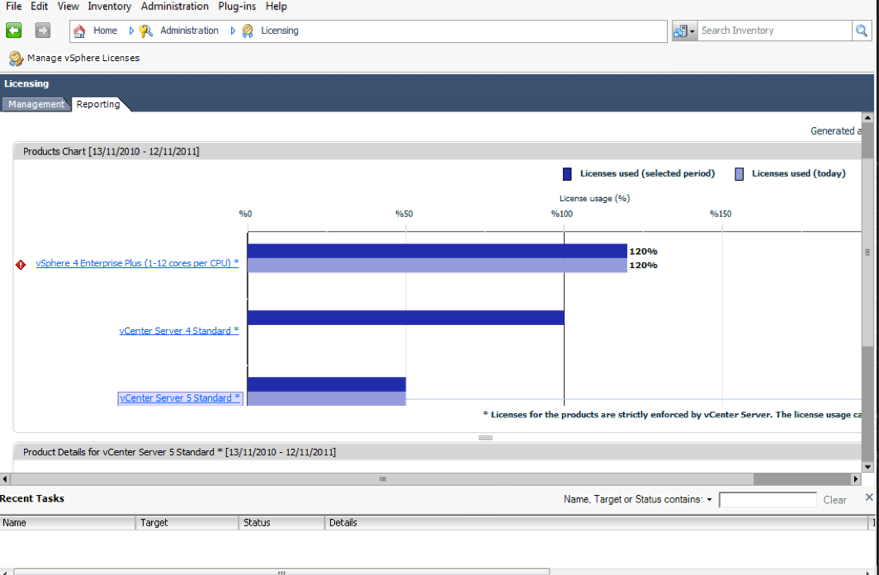
Licensing
Advanced licensing is no more, it is now only Standard, Enterprise and Enterprise plus. All license models are based on vRAM usage. (Amount of RAM currently active)
Each license type entitles you to a specific amount of vRAM per license you purchase.
The web client (server) needs to be installed in order to see the reporting of the vRAM pooled pricing in the licensing tab on vCenter.
Management
VMware have introduced some new management tools in vSphere 5. Most notably the vCenter Server Appliance and the Web Client.
vCenter Server Appliance
The new vCenter Server Appliance (vCSA) is based on SUSE linux enterprise server (SLES 11). It supports pretty much all the features available through the standard vCenter Server, which makes you wonder how long it will be until VMware will stop making a Windows OS based vCenter Server. This will of course mean no requirement for a Windows OS license or ‘standard’ vCenter Server install needs to be done, which will make deployment much quicker.
There is an optional embedded database, DB2 Express which supports 5 hosts/50 virtual machines and it also supports external Oracle database which adds support for 300 hosts/3000 virtual machines. It doesn’t support Microsoft SQL however. It also doesn’t support Linked Mode, vCenter Heartbeat, plug-ins or single sign on using Windows session credentials. Also the vCenter Storage Appliance (VSA) isn’t currently compatible with the vCSA.
The vCSA is configured through Web interface and can authenticate with Active Directory, you can also do initial configuration through a text based console, initial configuration such as network and time zone settings.
The vCenter Server Appliance default login is:
root
vmware
The vCSA is made available as an OVF template. It is made up of an appliance data disk and an appliance system disk.
Setting it up is very simple just go to vCenter Inventory Service on the console, click test settings and save settings on the vCenter database settings then start the vCenter Services on the vCSA virtual machine.
Further information see Configuring the VMware vCenter Server Appliance on the vSphere 5 Documentation Center
Web Client
The all new web client is built using Adobe Flex, the web client will be the future interface of vSphere administration, the current vSphere Client which is built with C# will be discontinued. To run it requires Internet Explorer version 7 or 8 or Firefox 3.5 or 3.6 and adobe flash 10 on both the client and server side.
At this moment in time no plug-ins are currently supported, however as this will be the client of the future I am certain that it will be added in a future update.
The web client is required on the vCenter Server in order to be able to view the vRAM pool utilisation report in the regular vSphere Client.
In order to use the web client you have to register it in the vCenter Server by going to the web client page as shown below.
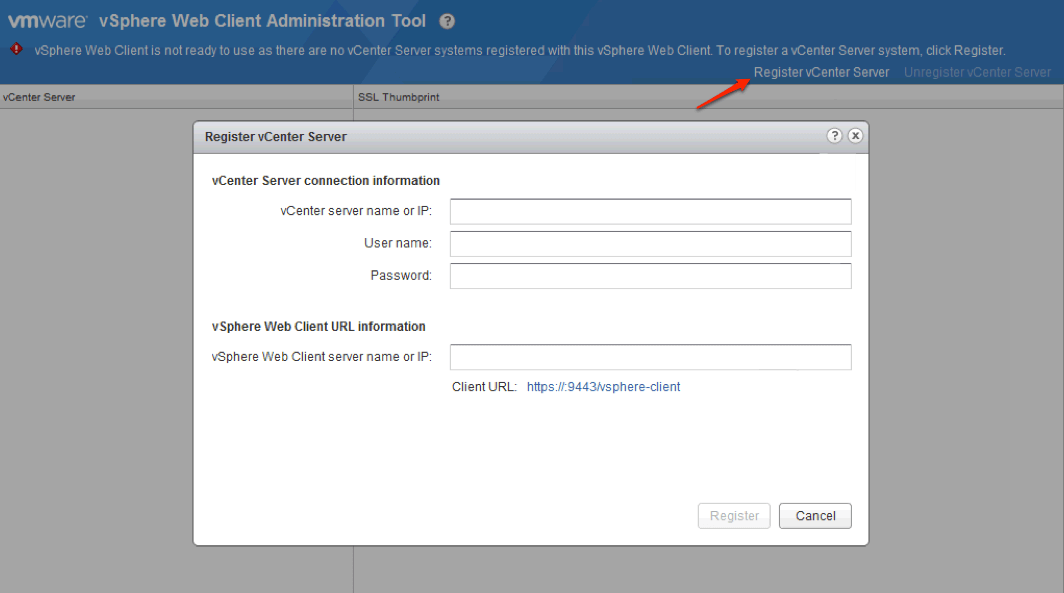
Once installed and configured you can do pretty much everything you can in the standard vSphere Client.
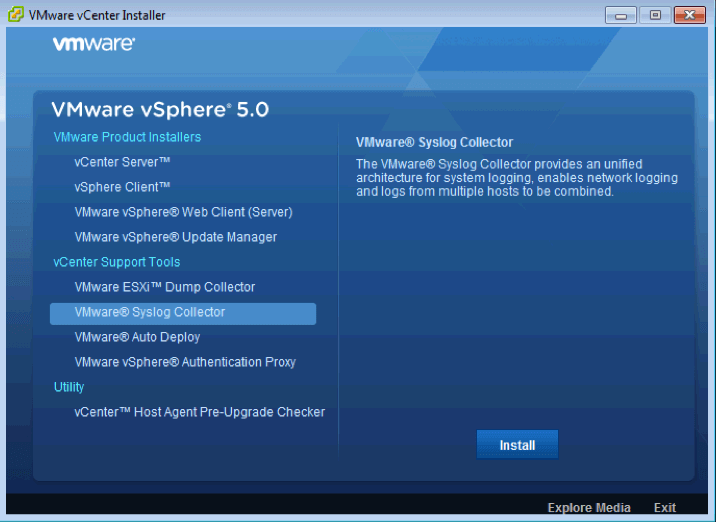
Syslog Collector
During setup you can create a syslog server, in fact ESXi will alert you to the fact that it hasn’t been configured until you set one.This can be any location and you can use the same location for multiple ESXi hosts. Just make sure it is somewhere off of the virtual infrastructure you are logging!
Networking
Firewall
To ensure protection from would-be hackers ESXi 5 now includes a firewall. Unlike the firewall previously used with ESX, this firewall is not based on iptables.
The new firewall is service-oriented and stateless. Users restrict access to specific services and ESXi maps the appropriate ports. This is configurable through the firewall section of the software settings area of the configuration tab is the vSphere Client.
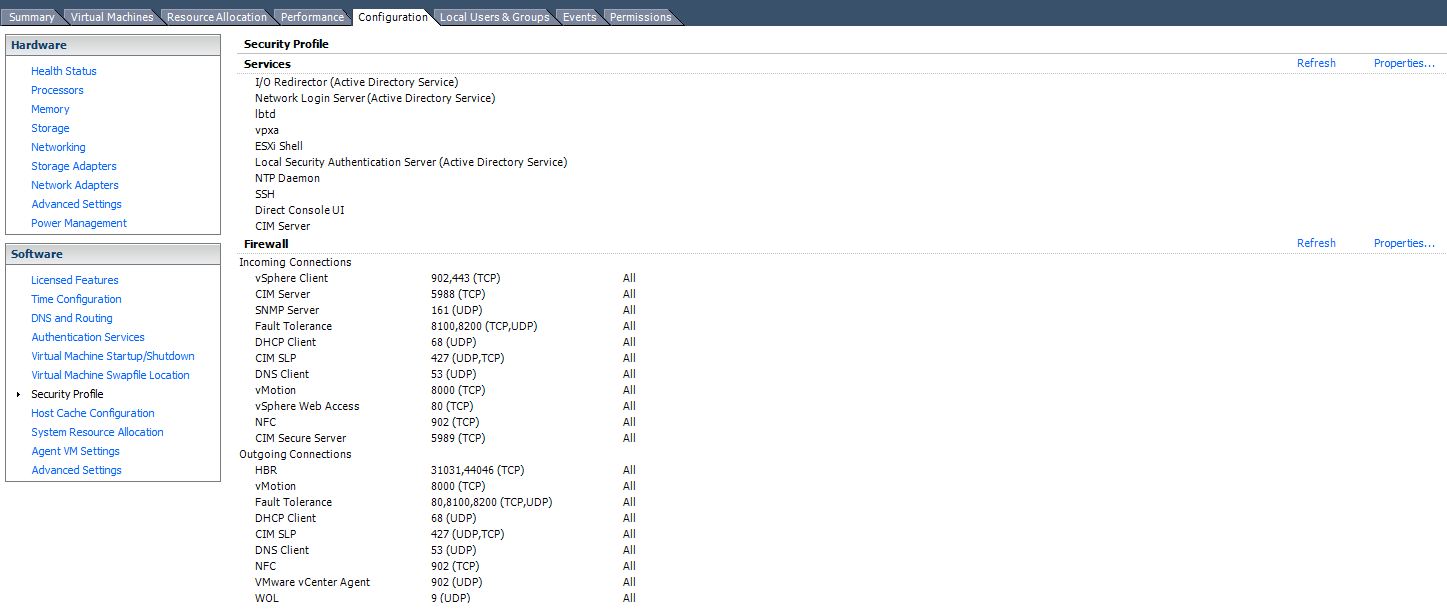
It is also possible to configure firewall settings and apply those to multiple hosts using host profiles.
The firewall can be configured through the command line using the five main options. Get, set, refresh, load and unload. It is now possible to restrict access from individual IPs or ranges rather than opening ports up to any traffic sources as was the case with previous versions.
New esxcli Network Firewall commands
get - Returns the status of the firewall
set-defaultaction - Updates default actions
set-enabled - Enables or disables the ESXi firewall
load - Loads the firewall module and rules
refresh - Refresh firewall configuration by reading the rule set files if the firewall module is loaded
unload - Destroy filters and unloads the firewall modules (Use with caution!)
ruleset list - List rule set information
ruleset set-allowedall - Sets the allowed all flag
ruleset set-enabled - Enables or disables the specified rule set
ruleset allowedip list - Lists the allowed IP addresses of the specified rule set
ruleset allowedip add - Allows access to the rule set from the specified IP address or range of IP addresses
ruleset allowedip remove - Removes access to the rule set from the specified IP address or range of IP addresses
Port Requirements
A few changes have been made to the port requirements. They required ports are shown in the table below.
dvSwitch
The dvswitch now supports Link Layer Discovery Protocol (LLDP), Netflow and Port Mirroring.
LLDP
LLDP enables VMware admins to see the configuration of physical switches. LLDP is set through the advanced settings of the dvswitch by choosing the options listen, advertise or both.
Netflow
Netflow helps to monitor the network to gain visibility of VM traffic. It can be used for profiling and billing purposes. It allows intrusion detection, network forensics and compliance. It sends networking data to a third party analyser. A flow is a unidirectional sequence of packets that share the same properties.
Netflow catches two types of flows:
- Internal flows - that is traffic on the same host
- External flows - traffic on different hosts, i.e. physical to virtual machines.
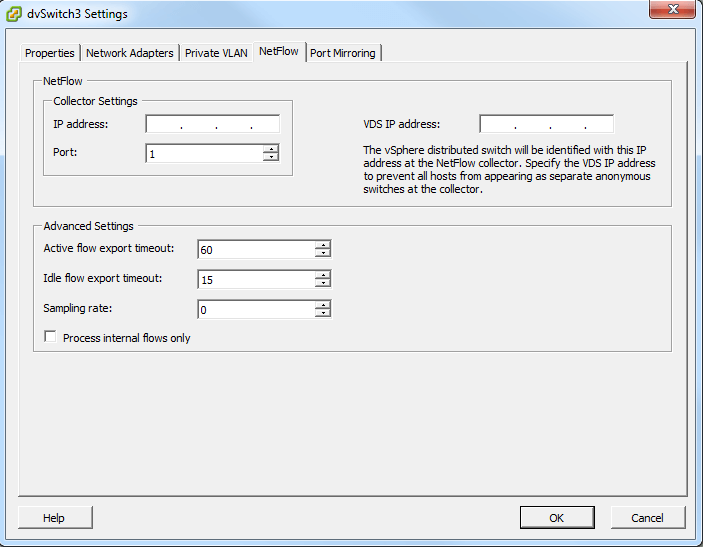
To configure go to dvSwitch settings and click on the Netflow tab and enter the Netflow collector settings.
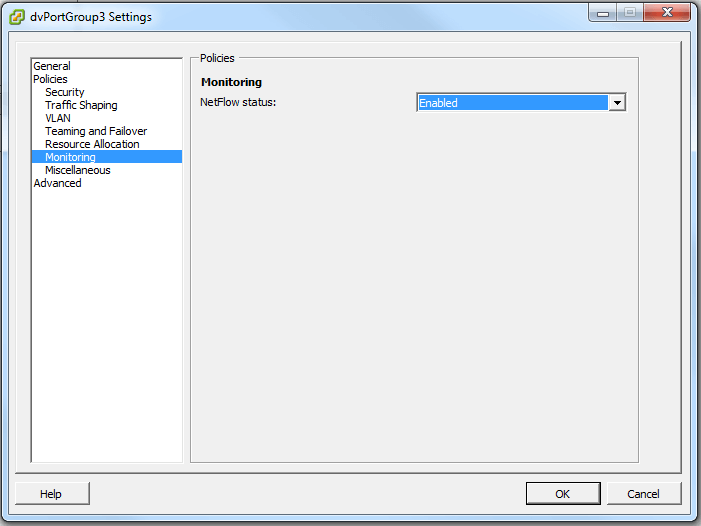
Once configured go to dvPortgroup settings>Monitoring>Netflow Status and set to enabled.
Port Mirroring
Port mirroring also referred to as Switch Port Analyser (SPAN) on Cisco switches send a copy of network packets seen on a switch port to a another switch port, i.e. sending mirrored data to a network monitoring device attached to a different port. Port mirroring overcomes the limitations associated with promiscuous mode. This can be useful for admins who need granular network information to troubleshoot network issues. This works in the same way as it does for the physical switches in the environment.
Network IO Control (NIOC) Enhancements
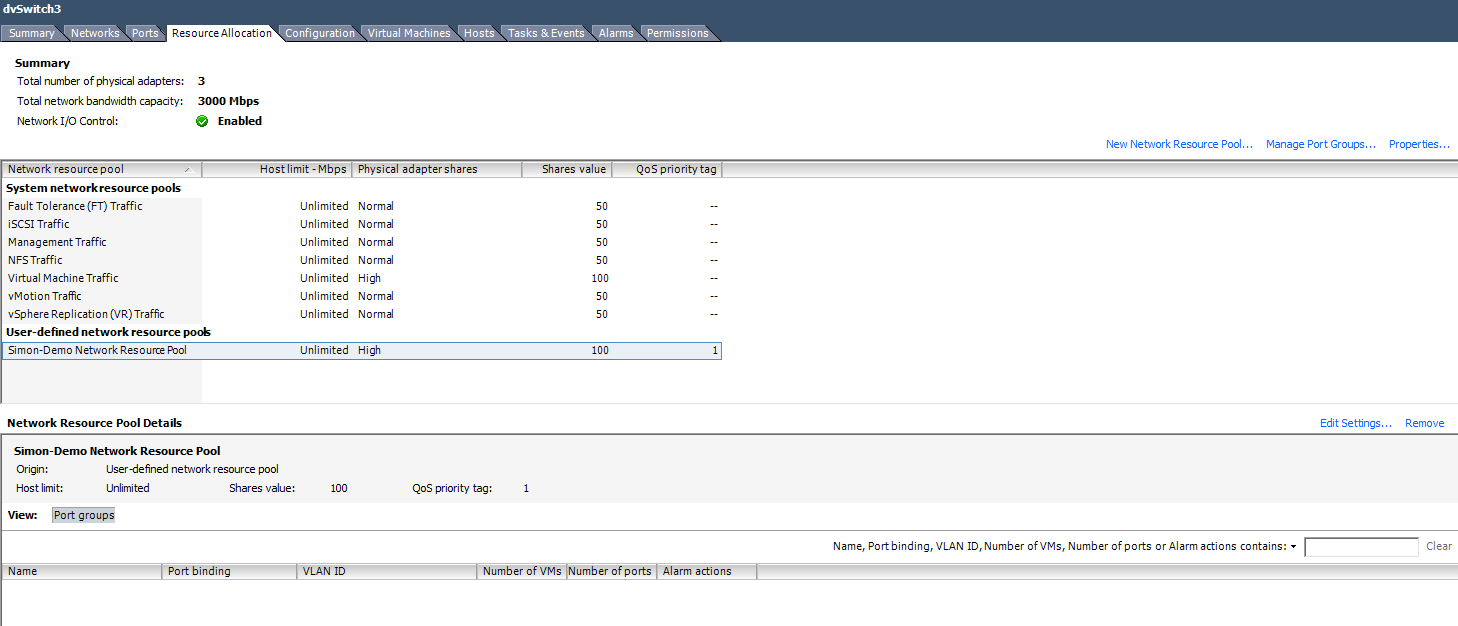
Network IO Control splits traffic into resource pools which can be prioritised. This was introduced in vSphere 4.1, however vSphere 5 has introduced features such as user-defined resource pools, IP tagging and a bandwidth ‘cop’ for HBR (Host Based Replication) traffic. (See Site Recovery Manager for more info on HBR)
User-defined network resource pools are similar to CPU and memory resource pools in that you can proiritise traffic I/O based on various requirements. These pools are set in the resource allocation tab of the dvSwitch.
Tagged with: vSphere
Comments are closed for this post.